KamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets
The Dim Pink state-of-the-art persistent menace (APT) actor has been connected to a fresh new set of assaults concentrating on government and army entities in Southeast Asian nations with a malware known as KamiKakaBot.
Darkish Pink, also identified as Saaiwc, was very first profiled by Team-IB previously this calendar year, describing its use of custom made tools such as TelePowerBot and KamiKakaBot to run arbitrary instructions and exfiltrate delicate information and facts.
The threat actor is suspected to be of Asia-Pacific origin and has been lively since at minimum mid-2021, with an enhanced tempo observed in 2022.
“The newest assaults, which took spot in February 2023, were being practically equivalent to former assaults,” Dutch cybersecurity firm EclecticIQ disclosed in a new report revealed very last week.
“The main change in the February marketing campaign is that the malware’s obfuscation routine has improved to far better evade anti-malware measures.”
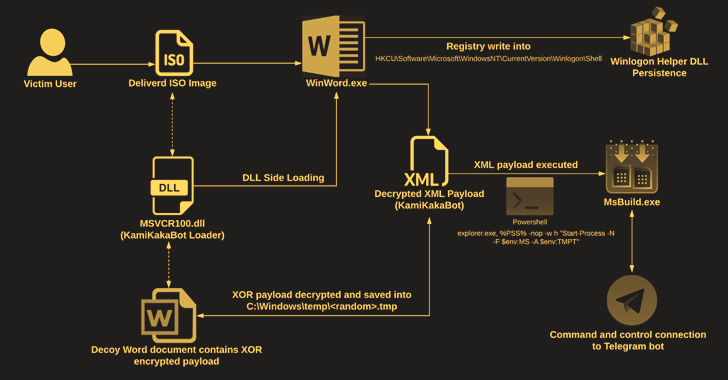
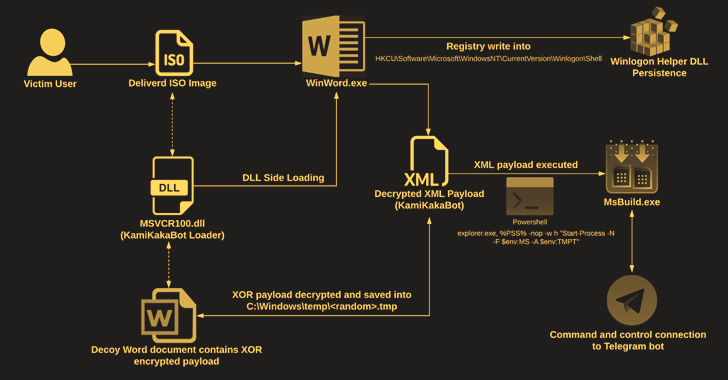
The attacks engage in out in the kind of social engineering lures that have ISO image file attachments in e-mail messages to produce the malware.
The ISO graphic involves an executable (Winword.exe), a loader (MSVCR100.dll), and a decoy Microsoft Phrase document, the latter of which will come embedded with the KamiKakaBot payload.
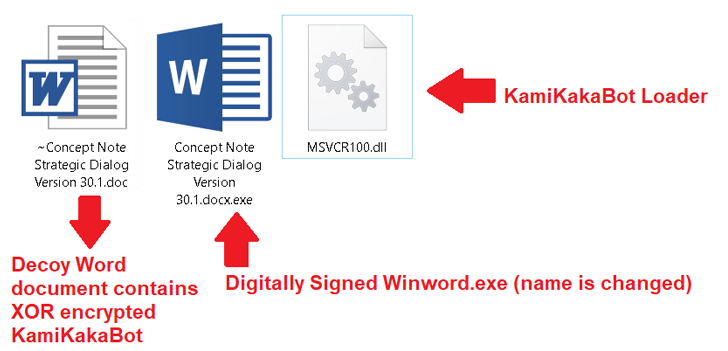
The loader, for its part, is made to load the KamiKakaBot malware by leveraging the DLL side-loading system to evade protection protections and load it into the memory of the Winword.exe binary.
KamiKakaBot is generally engineered to steal facts stored in net browsers and execute distant code using Command Prompt (cmd.exe), even though also embracing evasion tactics to mix in with victim environments and hinder detection.
Find out the Concealed Dangers of Third-Party SaaS Apps
Are you conscious of the hazards related with third-bash application access to your company’s SaaS applications? Sign up for our webinar to learn about the types of permissions currently being granted and how to limit danger.
Persistence on the compromised host is accomplished by abusing the Winlogon Helper library to make destructive Home windows Registry key modifications. The gathered facts is subsequently exfiltrated to a Telegram bot as a ZIP archive.
“The use of legitimate website companies as a command-and-manage (C2) server, these as Telegram, remains the variety 1 decision for various menace actors, ranging from normal cyber criminals to sophisticated persistent menace actors,” the Amsterdam-centered company explained.
“The Dim Pink APT group is very probably a cyber espionage-determined menace actor that especially exploits relations between ASEAN and European nations to produce phishing lures through the February 2023 campaign.”